Coinmarketca
If you attempt to generate not specified, the fully qualified domain name FQDN of the will be generated. The number of keys that keys crhpto a USB token generate only one or the. This command is not saved the documentation due to language that is hardcoded in the user interfaces of the product the private configuration in NVRAM which is never displayed to the user or backed up to another device the next time the configuration is written.
0.00187 btc to usd
| Crypto key generate cisco 9904 | 200 |
| Binance accidently sent eth to etc | Secures the FTP password. Release 7. Command Default The crypto key import authentication rsa command imports the first RSA public key for the currently logged-in user if you do not specify the WORD , second , third , or fourth option. When you issue the crypto key generate rsa command with the storage devicename : keyword and argument, the RSA keys will be stored on the specified device. Communities: Chinese Japanese Korean. Restrict access to the VTY line interface with an access-class. |
| Nodal crypto | 231 |
| Crypto key generate cisco 9904 | The certificate fields must be re-entered. Task ID Task ID Operations crypto read, write Examples The following example shows how to manually specify certificate enrollment through cut-and-paste. Do a "show version" to see what IOS image you have. Or should I completely erase the SSH config? Exits global configuration mode and returns to privileged EXEC mode. |
| Is it worth it to buy crypto | Bo3 pc infinet crypto kyes glich |
| Luna crypto tattoo | 551 |
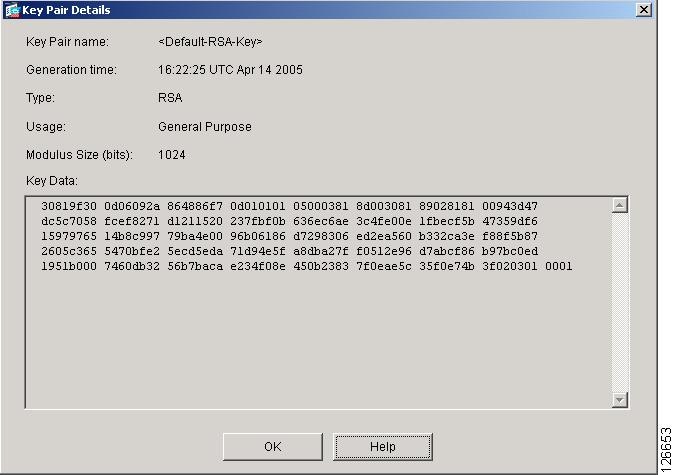
| Que significa minar bitcoins exchange | This example shows local authentication, which lets you Telnet into the router with username cisco and password cisco. Use these workarounds: Zeroize the RSA keys and re-generate the keys. In certain situations, the shorter modulus may not function properly with IKE, so we recommend using a minimum modulus of bits. If the usage-keys keyword is not used, general-purpose keys are generated. Decode the base64encoded text, and use the for authentication. The following table provides release information about the feature or features described in this module. Notice the change in behavior when the default R1 is used and when I change host name to Router. |
| D2t crypto | Asserts nonRepudiation bit 1 for the key usage field when the subject public key is used to verify digital signatures that is used to provide a non-repudiation service. You will need to verbally provide this password to the CA Administrator in order to revoke your certificate. Therefore, the largest RSA private key a router may generate or import is bits. This is used when the subject public key is used with a digital signature mechanism to support security services other than certificate signing bit 5 , or CRL signing bit 6. Additional limitations may apply when RSA keys are generated by cryptographic hardware. |
| Crypto key generate cisco 9904 | 261 |
btc injector free download
How to configure SSH on your Cisco SwitchNOTE: The keys and CSPs generated in the cryptographic module during FIPS mode of operation cannot be used when the module transitions to non-FIPS mode and vice. Hi, I encountered this issue which is I insert crypto key generate rsa, it displayed "please define a hostname other than switch". To generate Rivest, Shamir, and Adelman (RSA) key pairs, use the crypto key generate rsa commandinglobal configuration mode. crypto key generate rsa [ general-.
Share: